Industry talks: Cybersecurity & Governance
Today’s blog looks back at two recent industry talks organised by our colleague Professor (Associate) Carlene Campbell, who organised two talks to allow our students to gain a deeper understanding of the contemporary challenges in Cybersecurity, data governance, and regulatory compliance. Exploring how modern cyberattacks operate and how organisations can prevent and respond to them.
Both sessions emphasised practical examples, case studies, and interactive discussion to help our students better understand the real nature of the topics in industry and their future professional responsibilities.
Talk 1: From Code to Industry: Data Security, Governance and Compliance in the Real World
Delivered by Dr Odayne Haughton, Lecturer in Information Science at the School of Computing & Creative Technologies (University of West England)
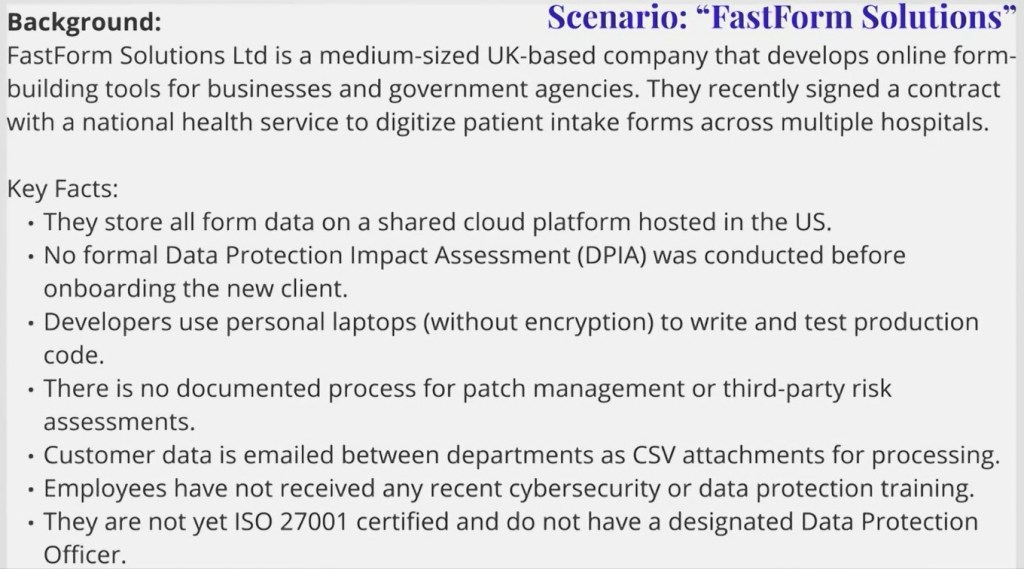
This talk introduced students to the practical realities of managing data securely and responsibly within modern organisations. Rather than viewing security incidents solely as technical failures, the session highlighted how many major data breaches are rooted in weak governance structures, unclear accountability, and poor compliance practices.




Key themes and topics:
- The three pillars of data responsibility: clear differentiation between data security, data governance, and regulatory compliance, and why none of these can operate effectively in isolation.
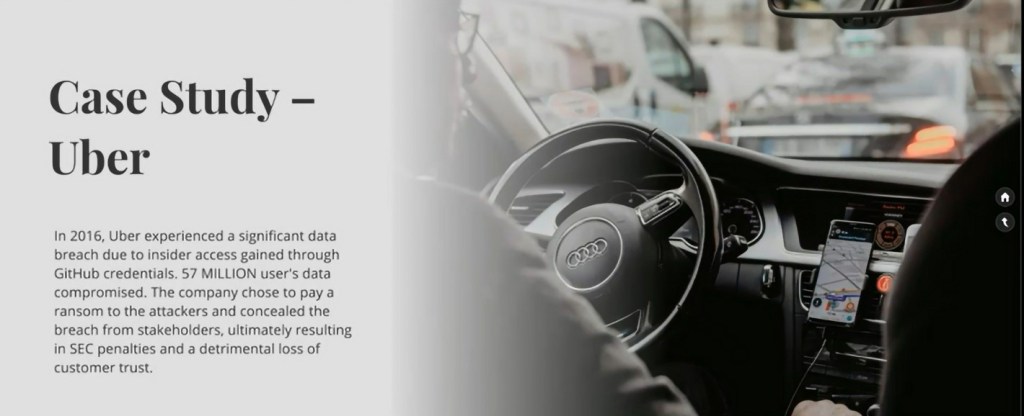
- Breaches as governance failures: analysis of real‑world incidents such as Equifax and Uber to demonstrate how cultural, procedural, and oversight issues often underpin technical compromise.
- Regulatory and standards landscape: introduction to GDPR and UK GDPR, ISO/IEC 27001 and 27701, and the NIST Cybersecurity Framework, with a focus on what these mean in day‑to‑day professional practice.
- Ethical implications: discussion of how poor compliance can result in misuse of personal data, bias, and long‑term damage to public trust.
- Security by design and compliance by default: embedding governance into the software development lifecycle using logging, encryption, audit trails, access control, MFA, and management of third‑party risk.
Interactive Activity:
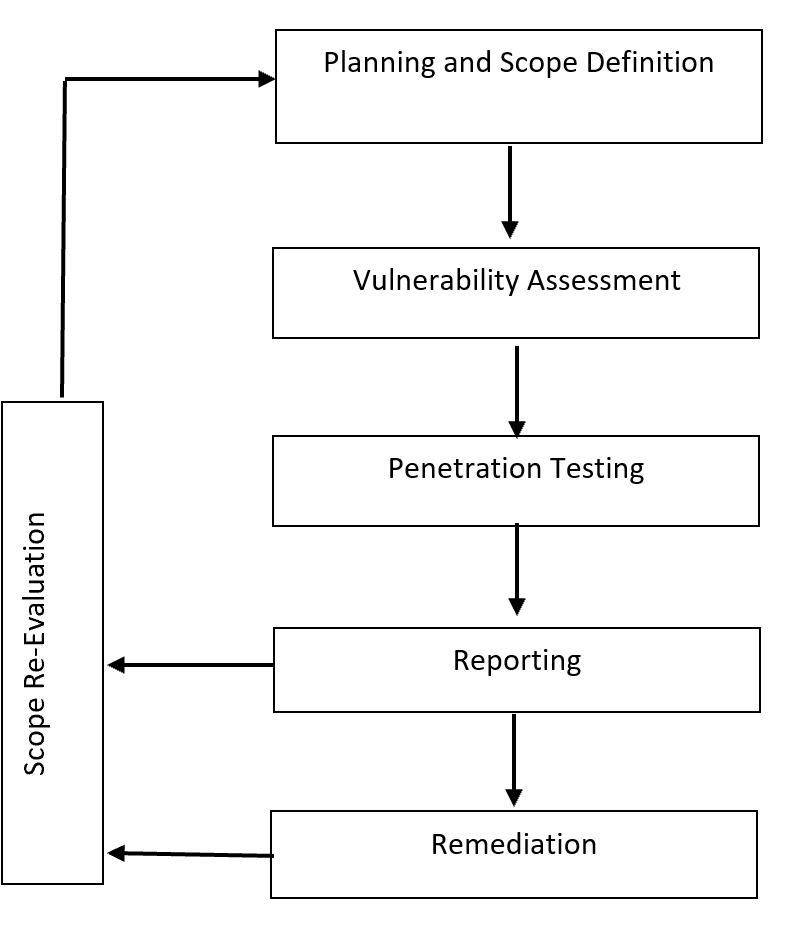
A group‑based scenario formed a central part of the session. Students worked through a simulated cloud‑services breach, taking on roles such as Data Protection Officer, Security Lead, Developer, and Product Owner. The exercise required them to identify governance failures, compliance violations, and immediate remediation steps, reinforcing the need for cross‑functional collaboration.
Key takeaway:
Students left the session with the understanding that data breaches are rarely caused by code alone. Effective data protection depends on governance structures, organisational culture, and shared responsibility across technical and non‑technical roles, and failures in these areas can have lasting legal, financial, and reputational consequences.
“The Guest Lecture introduced students to the practical realities of managing data security, governance, and regulatory compliance in modern computing environments. With a strong focus on real-world breaches, emerging global standards, and compliance requirements. The session bridged the gap between academic learning and professional responsibilities in industry.” – Carlene Campbell (Professor (Associate) at UWTSD’s School of Applied Computing.
Talk 2: Cybersecurity Awareness in the Modern Era
– Understanding how modern Cyber attacks happen and how we stop them
Delivered by Vignesh Balasubramanian (Director and co-founder of Sentronyx Technologies Pvt. Ltd) and Amit Shrivastav (A Cybersecurity professional & Senior Security Analyst at Sentronyx Technologies)
The second talk focused on helping students understand how and why modern cyberattacks occur, and how organisations attempt to defend against them. Framed within the realities of cloud adoption, hybrid working, and AI‑enabled tooling, the session positioned cybersecurity as both a technical and human challenge.


Key themes and topics:
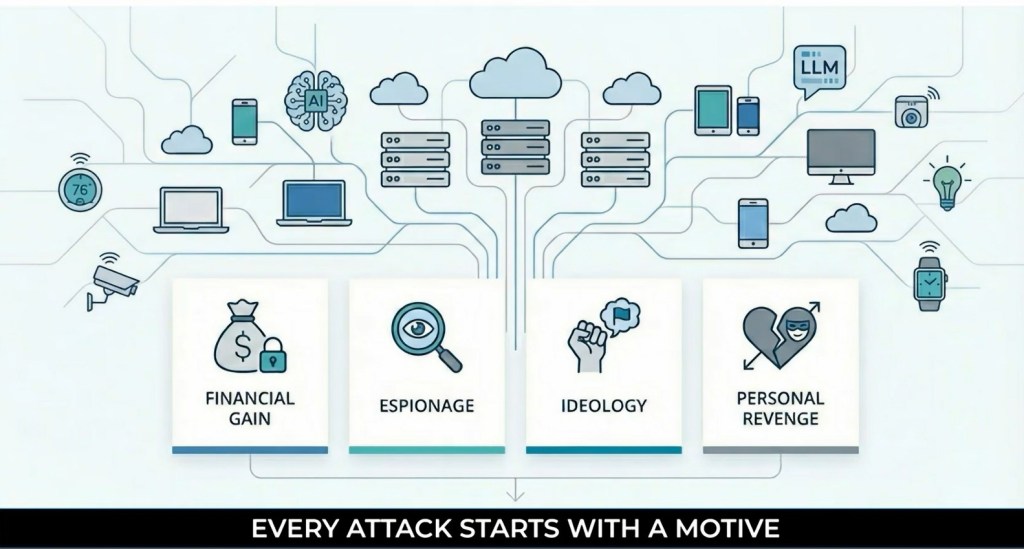
- Why cyberattacks happen: exploration of attacker motivations including financial gain, disruption, revenge, and curiosity, and how these motivations shape attack strategies.
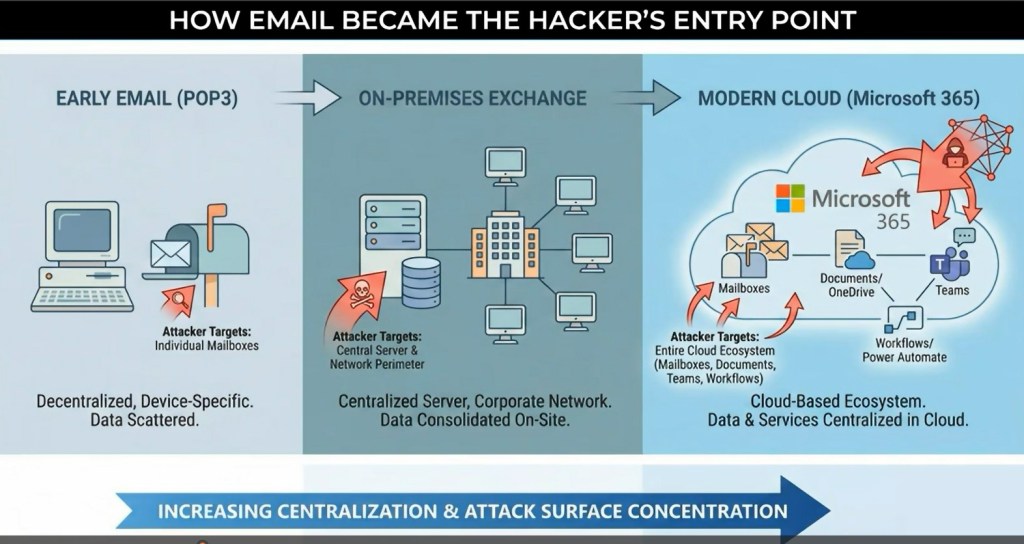
- Modern business infrastructure: overview of contemporary environments including cloud platforms, identity systems, endpoints, and collaboration tools, alongside the role of human behaviour in security outcomes.
- Evolution of authentication: progression from passwords to MFA, biometrics, and adaptive authentication, and the parallel evolution of attacker techniques such as phishing kits, token theft, session hijacking, and MFA bypass.
- Applied attack case study: detailed examination of Microsoft 365 MFA bypass frameworks, providing real‑world examples of account takeover and the global implications for organisations.
- Defence in depth: discussion of countermeasures including secure authentication design, user awareness, zero‑trust principles, and detection strategies.
- Offensive and defensive collaboration: the role of red and blue teams, and how leadership decisions shape an organisation’s overall security posture.
Interactive discussion:
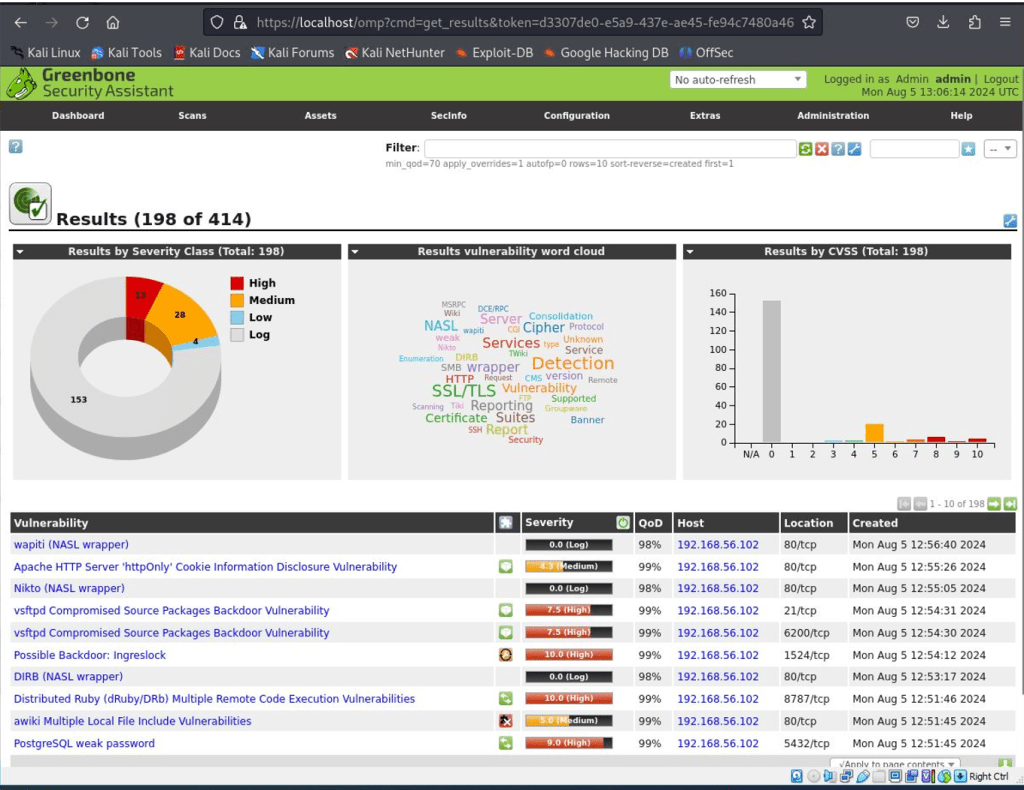
The session included open Q&A and practical discussion, allowing students to explore topics such as phishing detection, threat simulation, and attack surface analysis in a real‑world context.
Key takeaway:
Students gained a clearer picture of cybersecurity as an ongoing contest between attackers and defenders, where technology alone is insufficient. Awareness, collaboration, and informed leadership are essential to building resilient organisations in a rapidly evolving threat landscape.
“This guest lecture used a number of live demonstrations to help students understand how and why modern cyberattacks occur, how attackers evolve to bypass defenses, and how ethical hacking contributes to stronger cybersecurity. It explored real-world attack techniques, and the critical role of offensive and defensive security activities in building resilient organizations.” – Carlene Campbell (Professor (Associate) at UWTSD’s School of Applied Computing.
Final Remarks:
Both talks strengthened our students exposure to real‑world practice, offered a complementary view of modern digital risk, from governance and regulatory responsibility to the tactics used in real‑world cyberattacks. By grounding theory in industry practice and interactive learning, the sessions reinforced the importance cybersecurity and data protection as imperative organisation‑wide concerns.
For more information about our Computing & CyberSecurity courses please click here: Computing | University of Wales Trinity Saint David